Blue Team Labs Online - Enter The Dragon

You have been tasked with performing static disassembly of the executable. Due to time constraints the only tool available is Ghidra.
Reverse Engineering
Tags: Ghidra T1547.001 T1622
Scenario A customer has activated their incident response retainer following the discovery of a suspected malicious executable on one of their hosts. The executable was detected during routine Security Operation Centre (SOC) threat hunt activities. SOC analysts have performed basic static analysis of the executable but were unable to identify any Indicators of Compromise (IOCs).
You have been tasked with performing static disassembly of the executable. Due to time constraints the only tool available is Ghidra.
Environment Awareness
Evidence & Tool Discovery
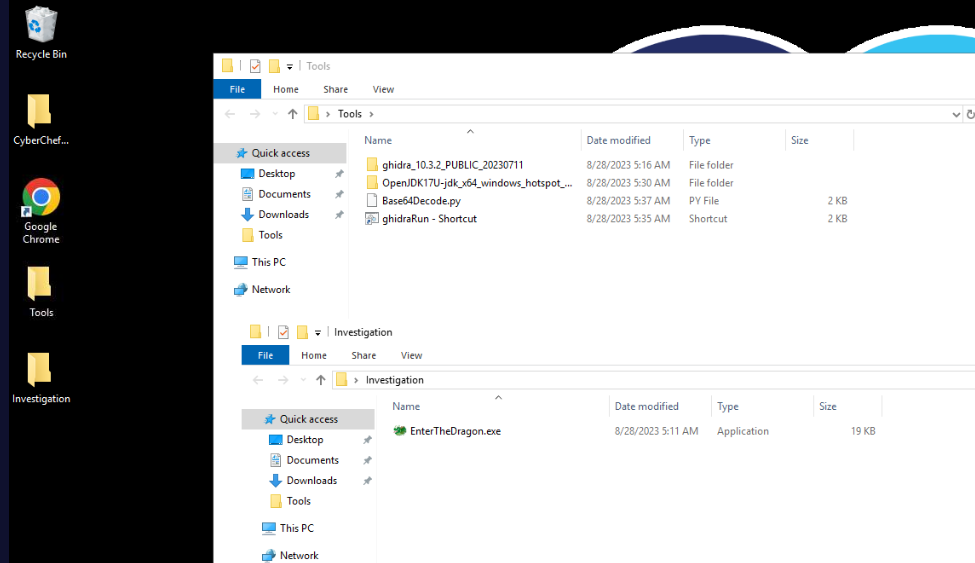
On this investigation machine, we have a malware sample inside Tools folder on the desktop and we only have Ghidra and Cyberchef available so we will have to conduct static analyse this malware.
Investigation
Q1) What is the MD5 of the executable? (Format: MD5)
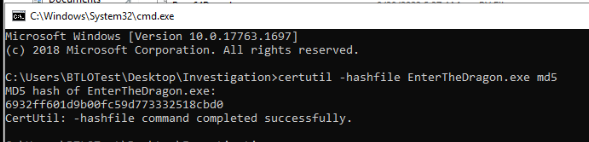
Lets use Windows lolbin to generate file hash such as certutil with certutil -hashfile EnterTheDragon.exe md5 then we will have MD5 hash of this file (we have to specify hash algorithm for certutil since it will generate SHA1 hash by default)
Alternative to this is a Get-FileHash cmdlet on PowerShell that you can use Get-FileHash .\EnterTheDragon.exe -Algorithm MD5 to get MD5 hash of this file (we have to specify hash algorithm for Get-FileHash cmdlet since it will generate SHA256 hash by default)
Answer
6932ff601d9b00fc59d773332518cbd0Q2) What is the image base? (Format: 0xYYYYYYYYY)
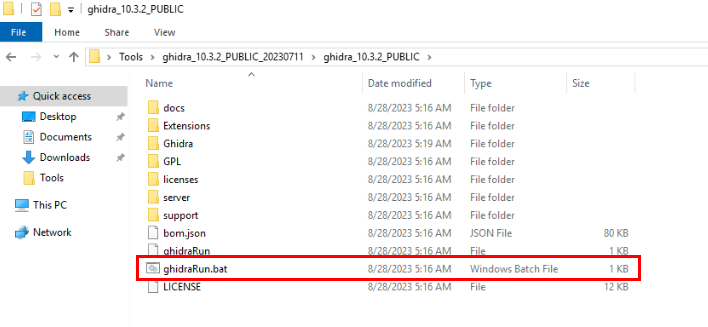
Lets import this file into Ghidra, First we need to run Ghidra but execute ghidraRun.bat script
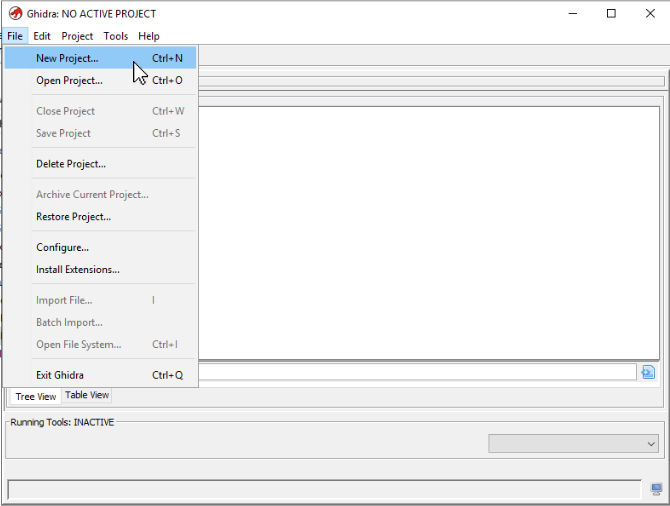
Then we have to create "Non-Share Project" to work on Ghidra.
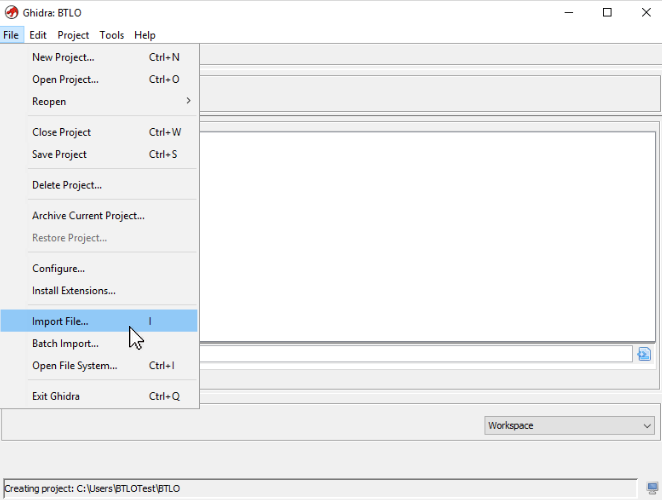
After created a project, its time to import the sample.
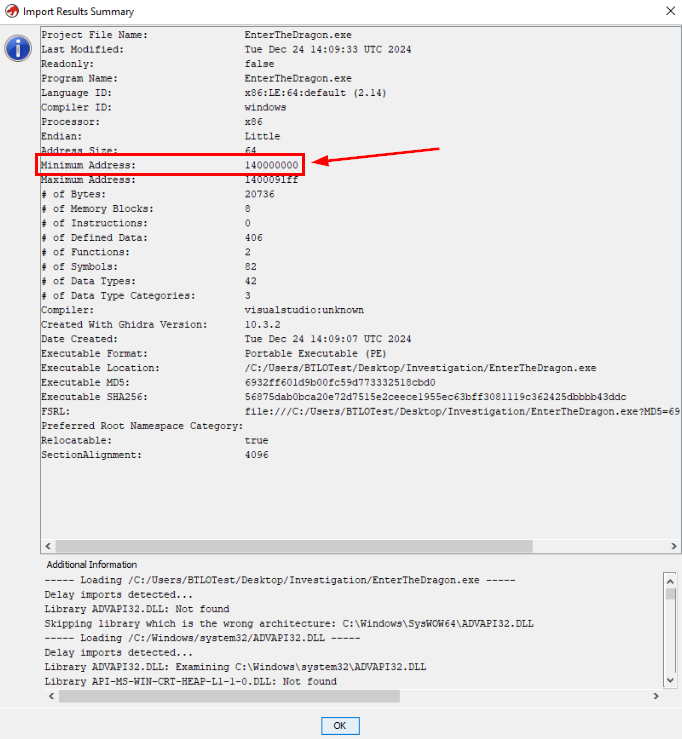
After imported a file, we will have "Import Results Summary" window shows up like this and we can see the minimum address of this file and it is where image base is located.
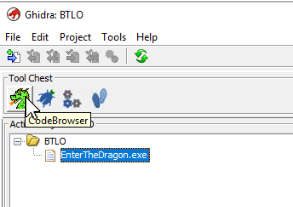
We can confirm this by open this file on Ghidra CodeBrowser
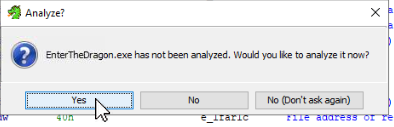
We will have to let Ghidra analyze this file first, just go with "Yes" and its default setting.
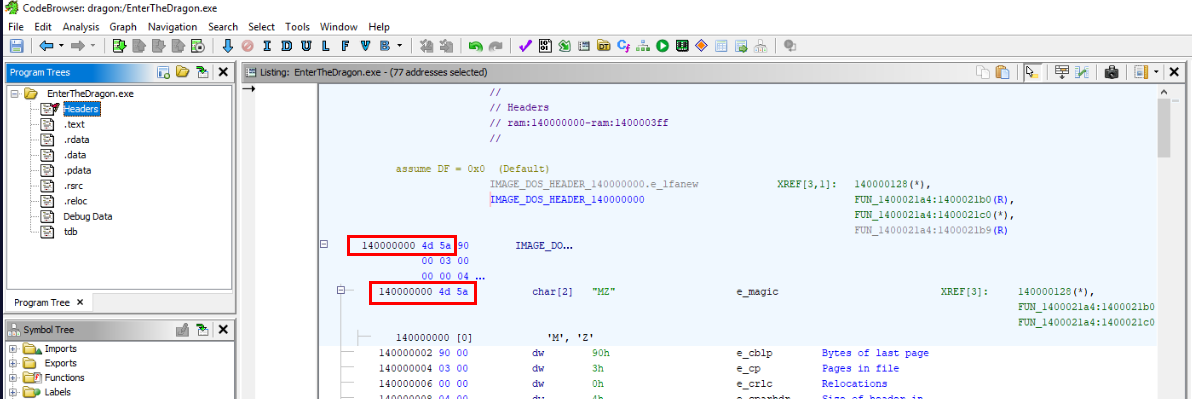
Now if we goes to "Header" which located at the minimum address of this executable, we can see that the image base address starts at MZ header which is a magic header for PE32 executable file.
Answer
0x14000000Q3) What is the RVA offset of the Entry Point? (Hint: RVA is Virtual Address (VA) – ImageBase) (Format: 0xYYYY)
The Entry Point is where the execution of a program begins so normally, a main function will be called by The Entry point
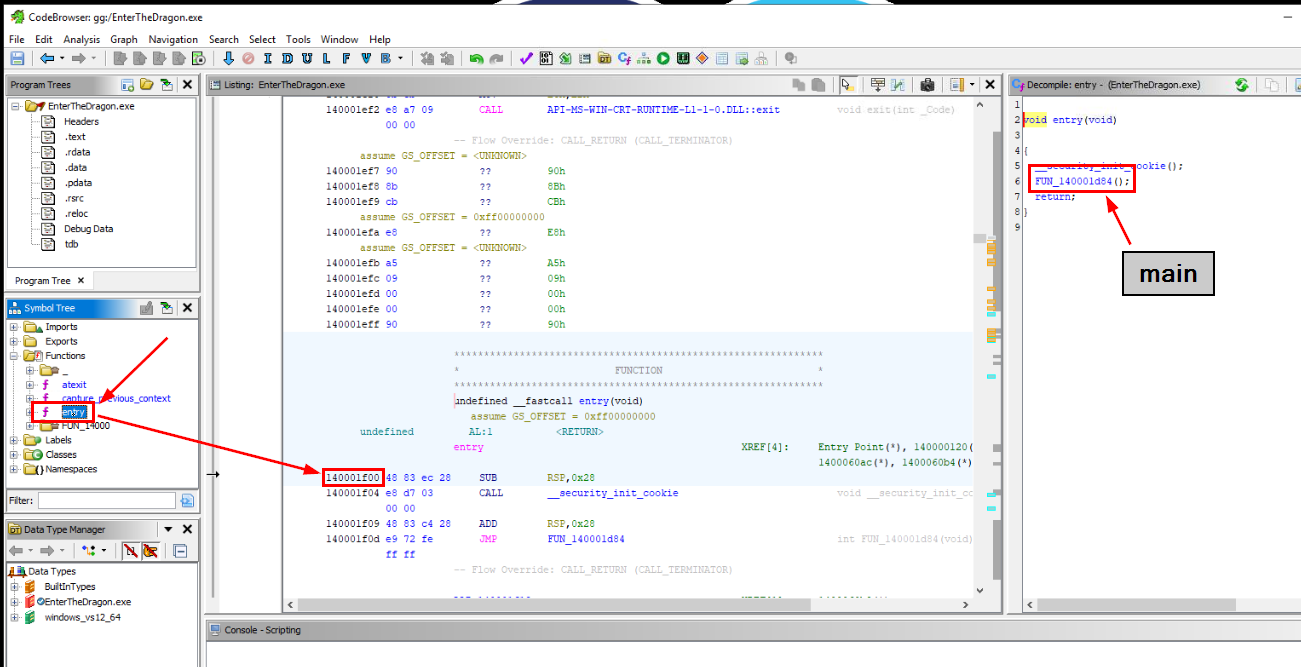
After analyzed a file using Ghidra, it usually jump to The Entry Point but if we have to go back to this function then we have to expand "Funtions" inside "Symbol Tree" window then find entry function
Which we can see that the address of this function on the binary is 0x14001f00 but RVA - Relative Virtual Address which is used to describe a memory offset if the base address (in this case 0x14000000) is unknown so if we remove the base address then we will have RVA address which is 0x1f00
Answer
0x1f00Q4) What is the first function called from the entry point? (Format: __somethingsomethingsomething)
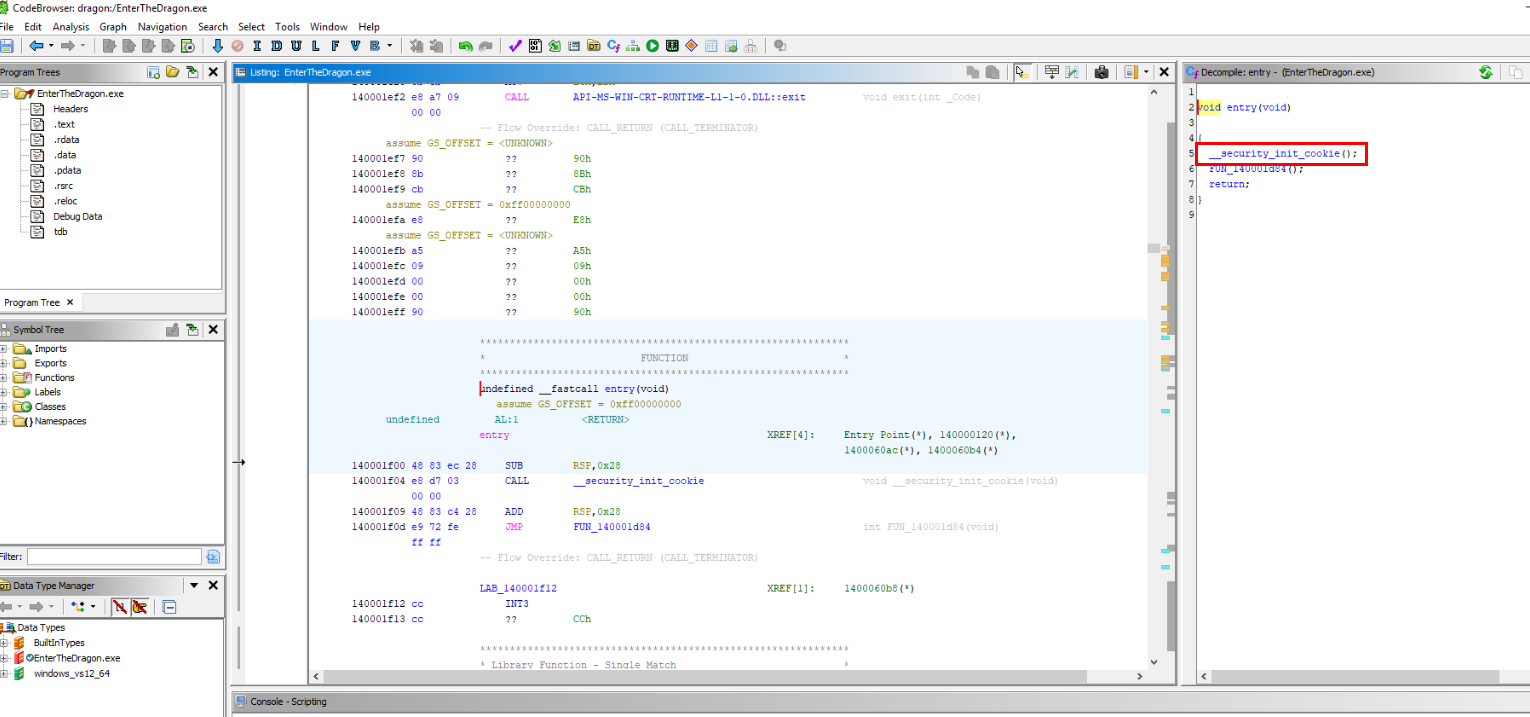
We can see that before it calls main function, it will call __securityinitcookie first which will initializes the global security cookie used by the compiler for runtime checks. (to detect unexpected memory modifications by validating its integrity.)
Answer
_security_init_cookieQ5) At what Virtual Address (VA) offset is IsDebuggerPresent() called? (Hint: VA is RVA + ImageBase) (Format: 0XYYYYYYYYY)
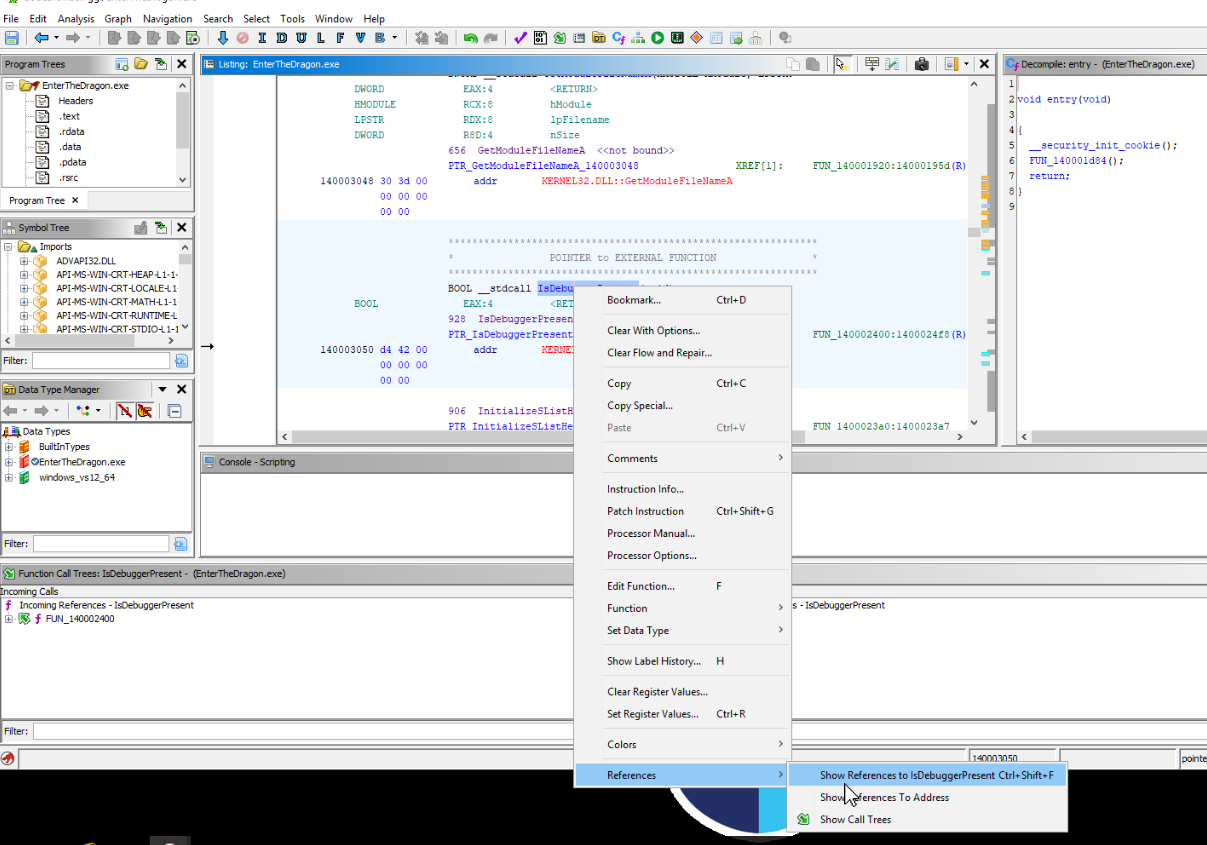
IsDebuggerPresent() is a function that was imported from kernal32.dll so we can utilize Symbol Tree to find for this imported address of this function and type Ctrl + Shift + F to show reference to this function (normally a function call should be return if a function is called)
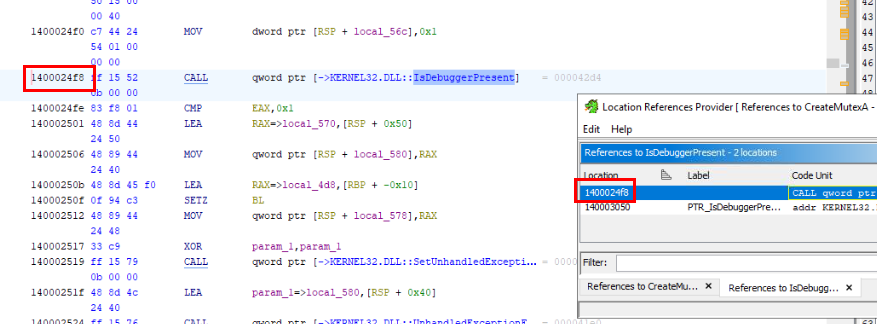
Then we can see the address that call for this function right here.
Answer
0x1400024f8Q6) How many functions are imported from WININET.DLL? (Format: Number)
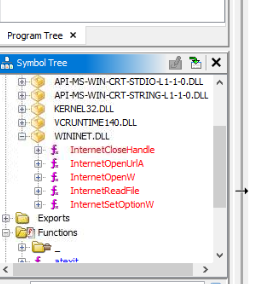
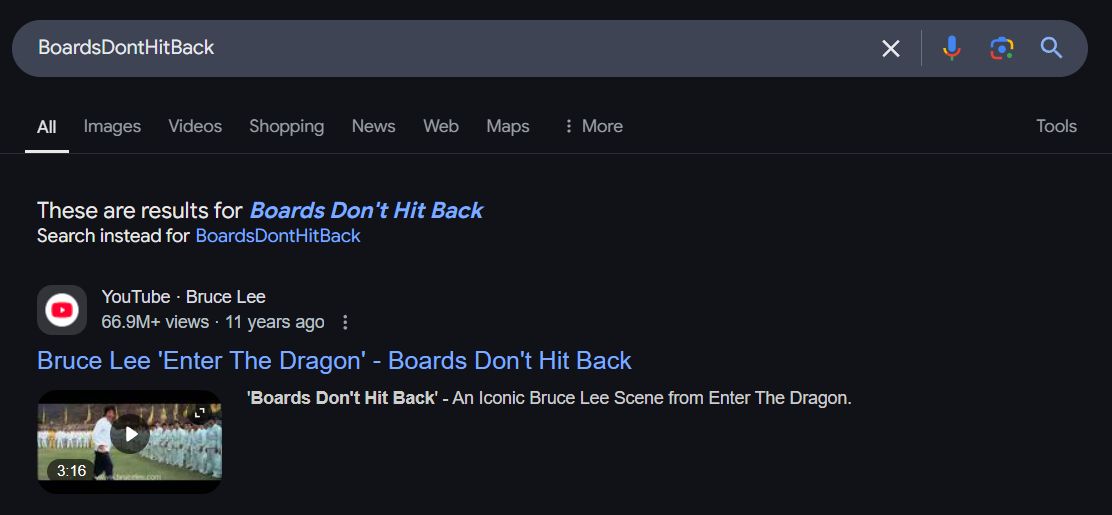
Utilized symbol tree, then we can see that there are 5 functions imported from WININET.dll
Answer
5Q7) What security attribute (LPSECURITY_ATTRIBUTES) is used when the mutex object is created? (Hint: Look at the KERNEL32.DLL if you’re stuck) (Format: 0XY)
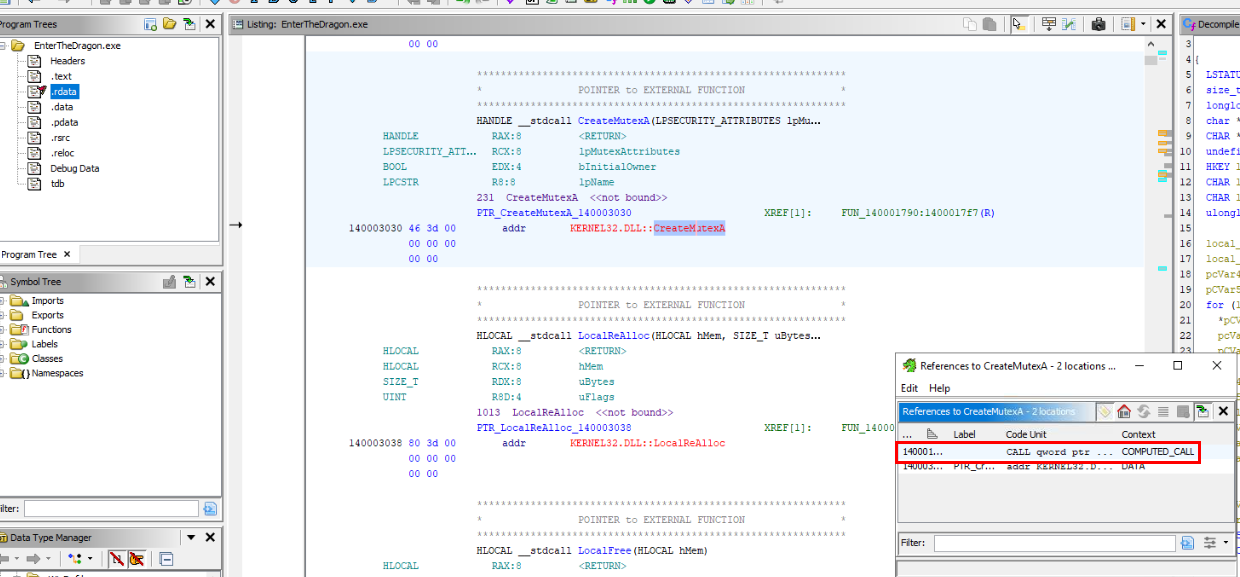
We can utilize "Show Reference" feature to find any function calls to CreateMutexA() function like this.
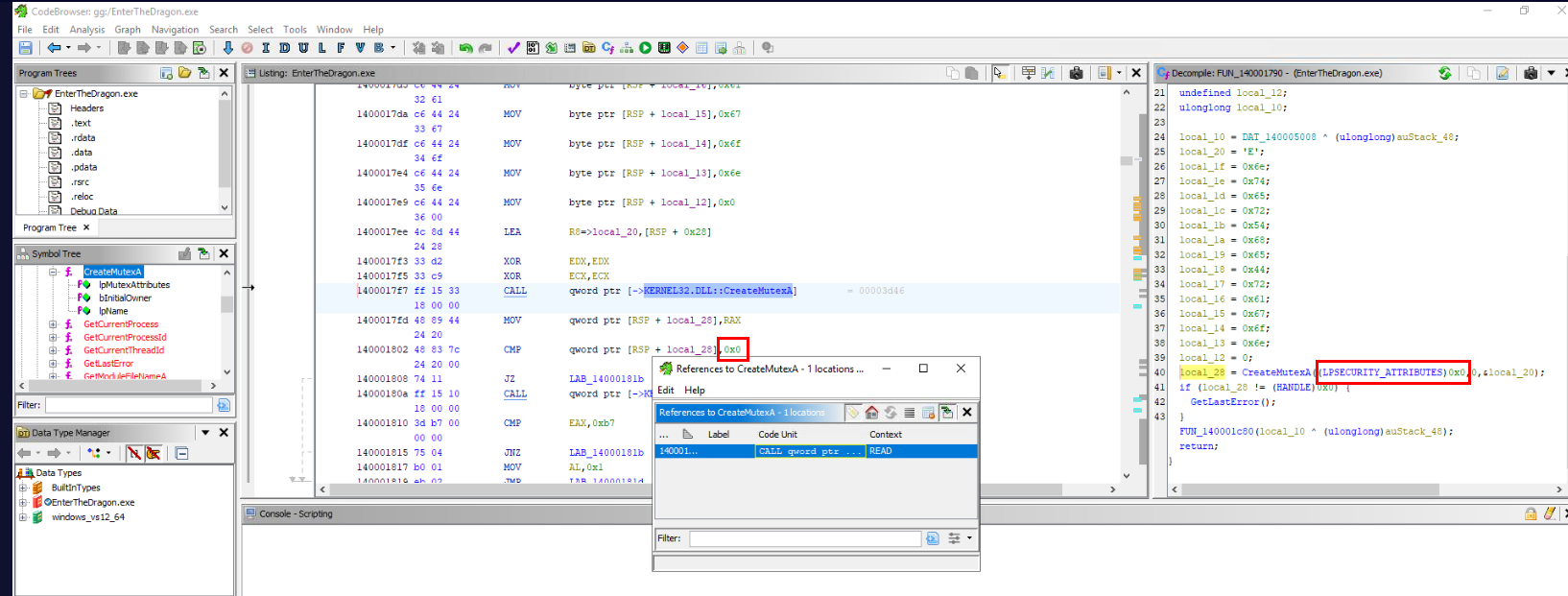
Then we can see that the first argument that pass to this function is LPSECURITY_ATTRIBUTES and it is set to 0x0 (null) indicates that default security settings are applied.
Answer
0x0Q8) What is the name of the mutex object? (Format: String)
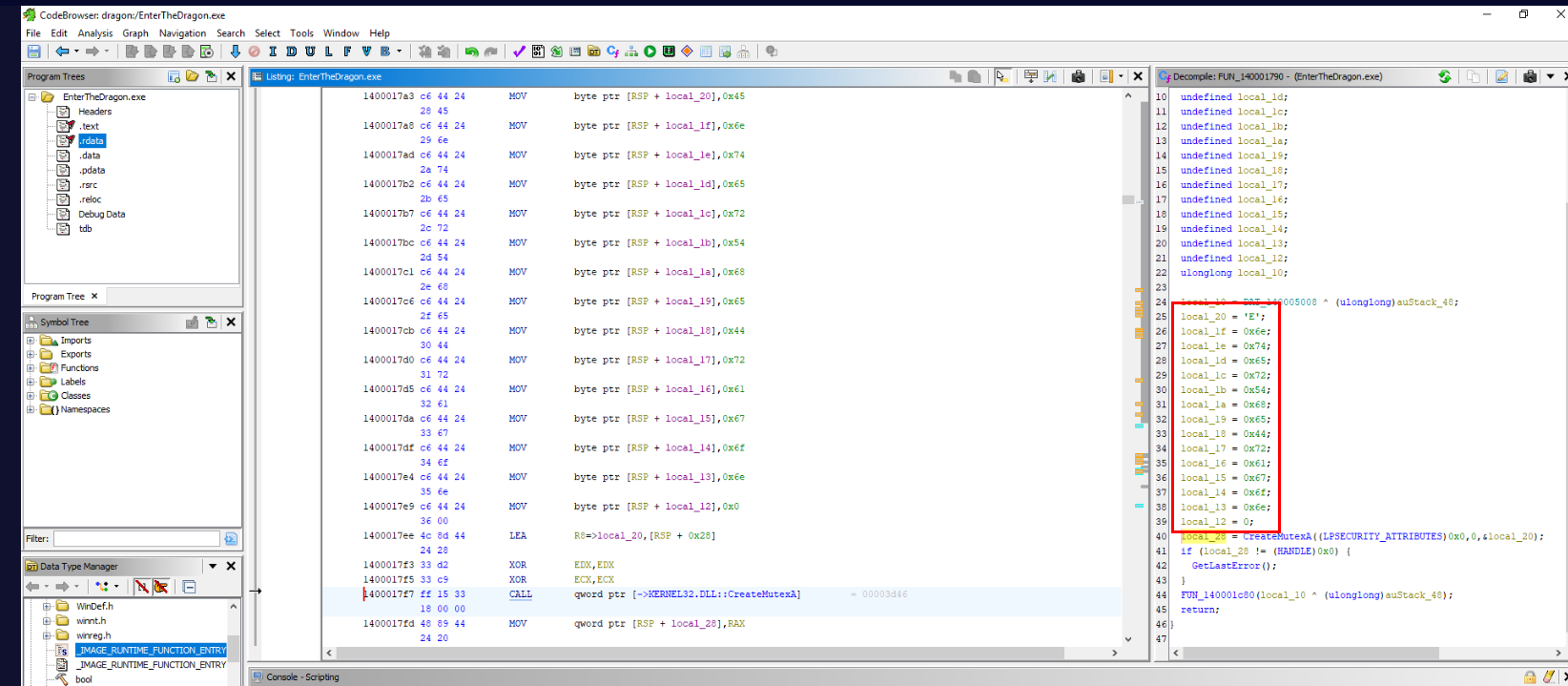
Name of the mutex is the third argument that pass to CreateMutexA function and from this sample, we have to concatenate these variables together.
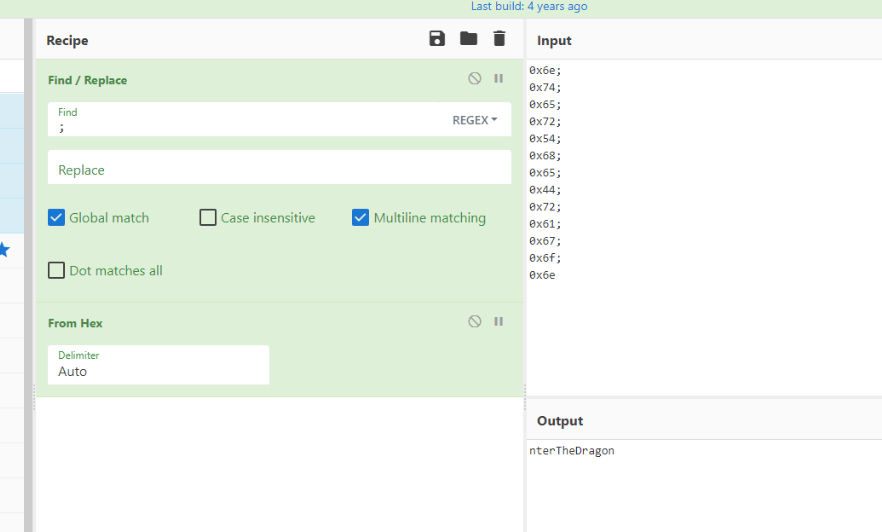
Then we can see that "EnterTheDragon" will be the name of this mutex.
Answer
EnterTheDragonQ9) Where does the sample copy itself to? (Hint: Look at the API-MS-WIN-CRT-STDIO-L 1-1-0.DLL if you’re stuck) (Format: C:\something\something.extension)
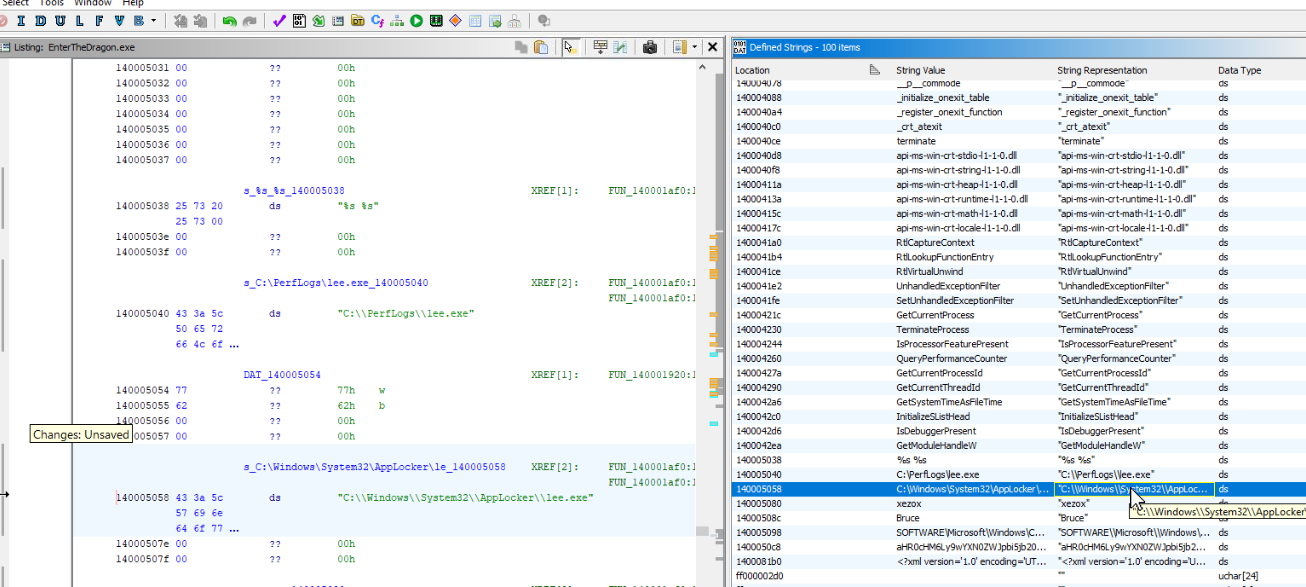
To save myself sometimes, I utilized "Defined Strings" feature to find any defined strings that look like a path and find its reference which we can see that we have 2 candidates right here.
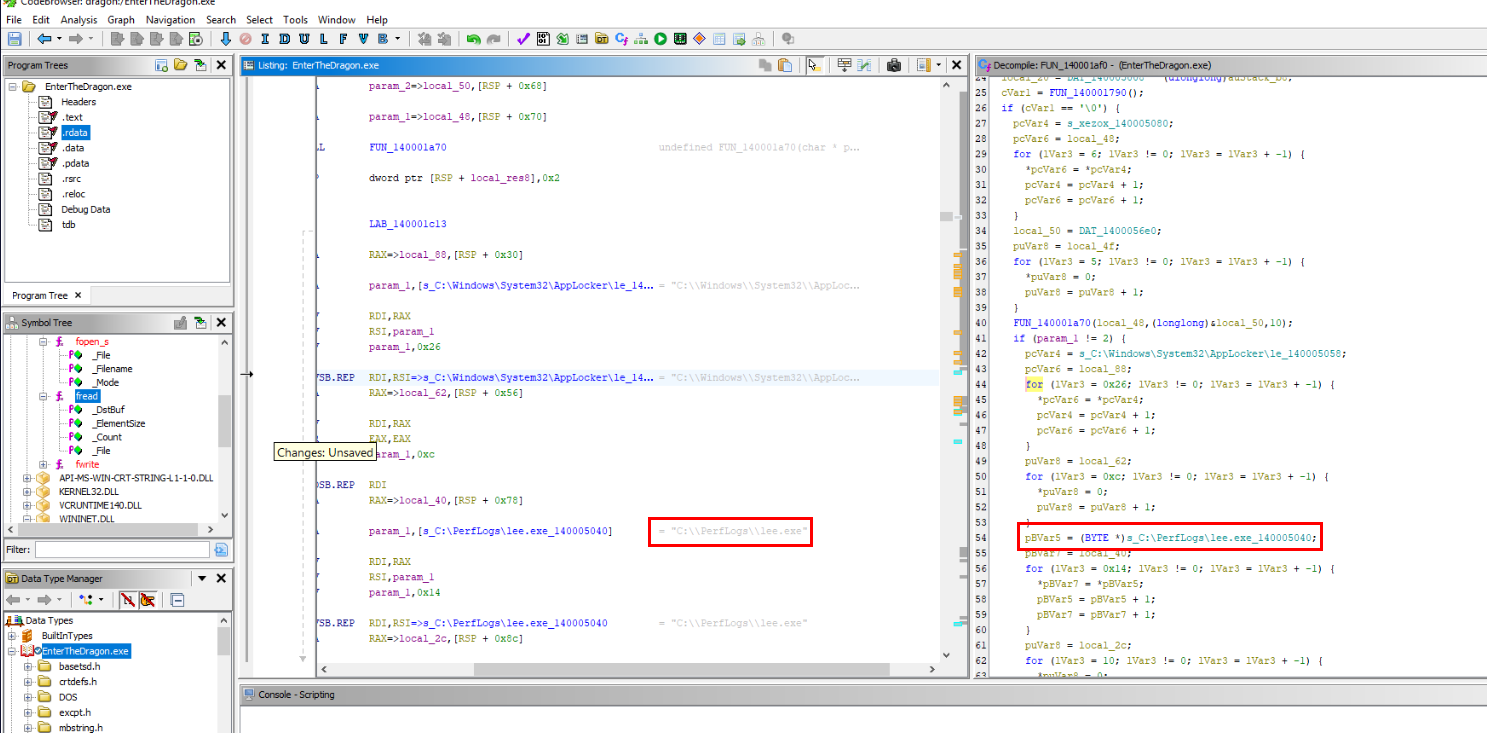
Which we can see that this path is where the sample will copy itself to.
Answer
C:\\PerfLogs\\lee.exeQ10) What size is the buffer used to perform the file read operation? (Format: XXXX)
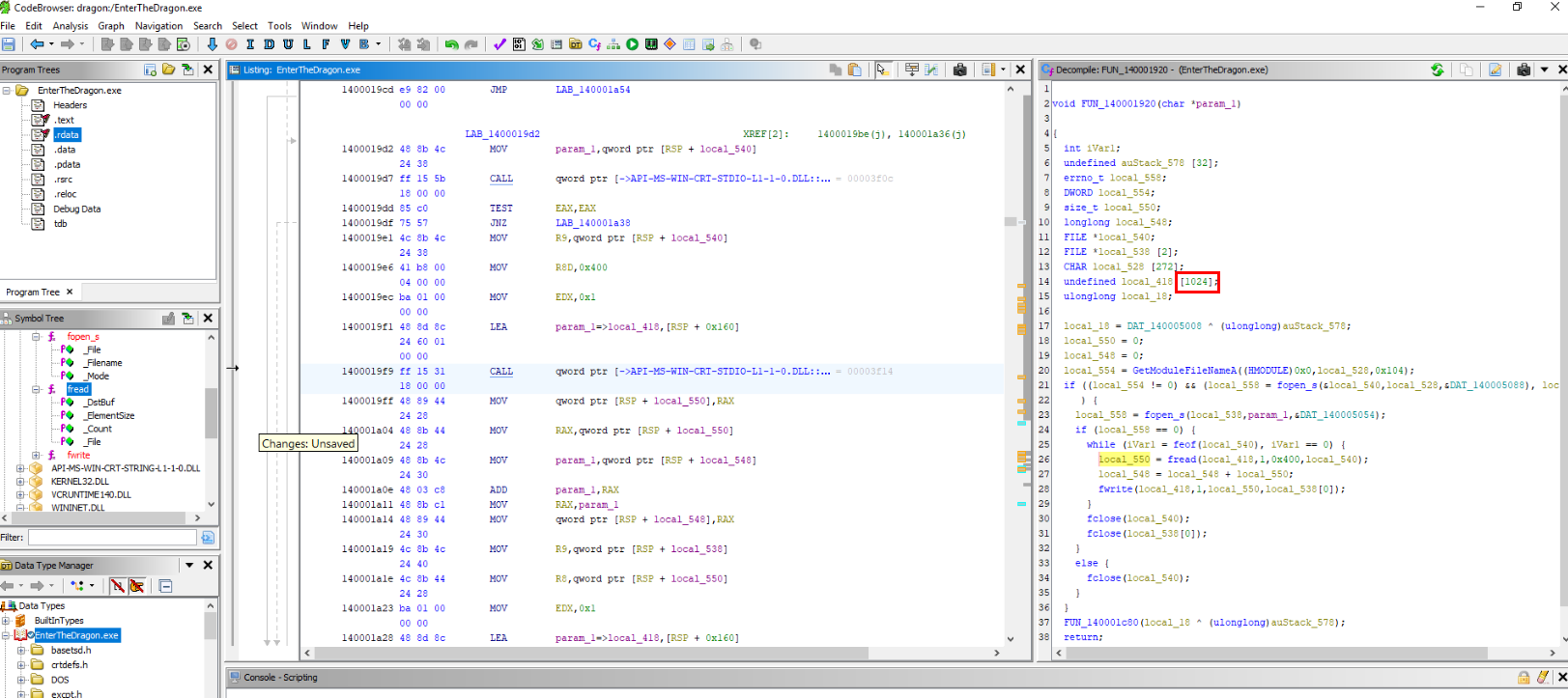
By tracing back the reference to fread() function, we can see that 1024 is a buffer sizes that used to perform file read operation by Fun_140001920() function
Answer
1024Q11) What encoding is used to obfuscate the payload URL? (Hint: Look at the WININIT.DLL if you’re stuck) (Format: Encoding Method)
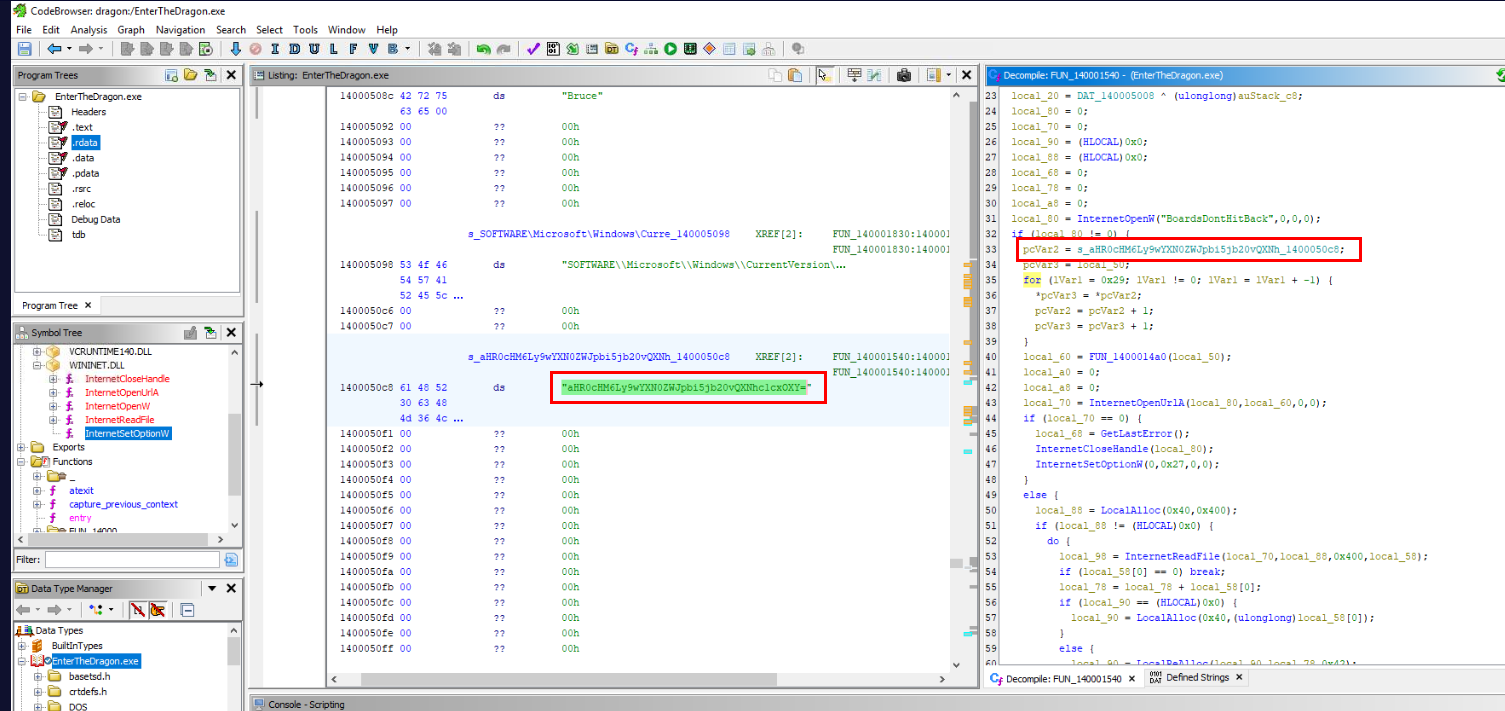
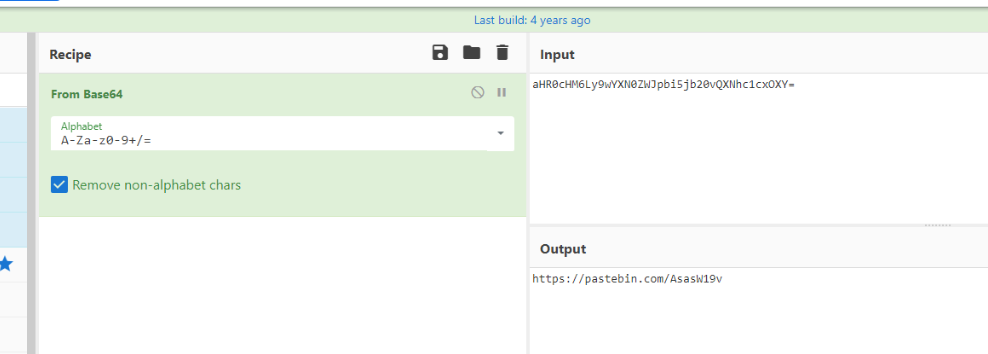
We can trace the reference to functions imported from WININIT.DLL then we can see that there is one string that look like it is encoded and we can see that it has = as padding indicates that it might be base64 encoded
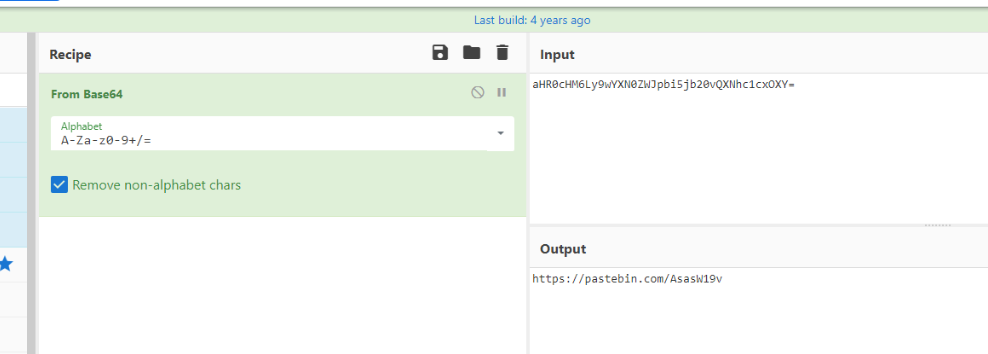
We can confirm this hypothesis by use From Base64 operation on CyberChef which reveal pastebin url which proved this hypothesis to be true.
Answer
base64Q12) What is the decoded URL? (Format: https://domain.tld/something)
Answer
https://pastebin.com/AsasW19vQ13) What is the user agent used during the URL access request? (Hint: Look at the WININIT.DLL if you’re stuck) (Format: String)
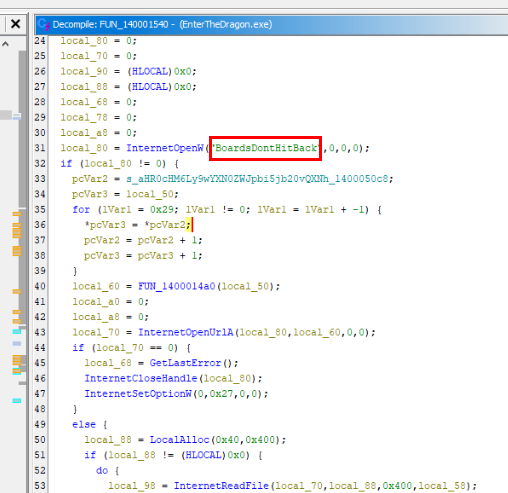
The first argument pass to InternetOpenW() function is a user-agent the will be used to create a connection in the HTTP protocol.
For those who do not get "What is Boards Don't Hit Back?", here is an explaination.
Answer
BoardsDontHitBackQ14) What is the registry path string used to establish persistence? (Hint: Start looking at the ADVAPI32.DLL if you’re stuck) (Format: HIVE\path\to\key)
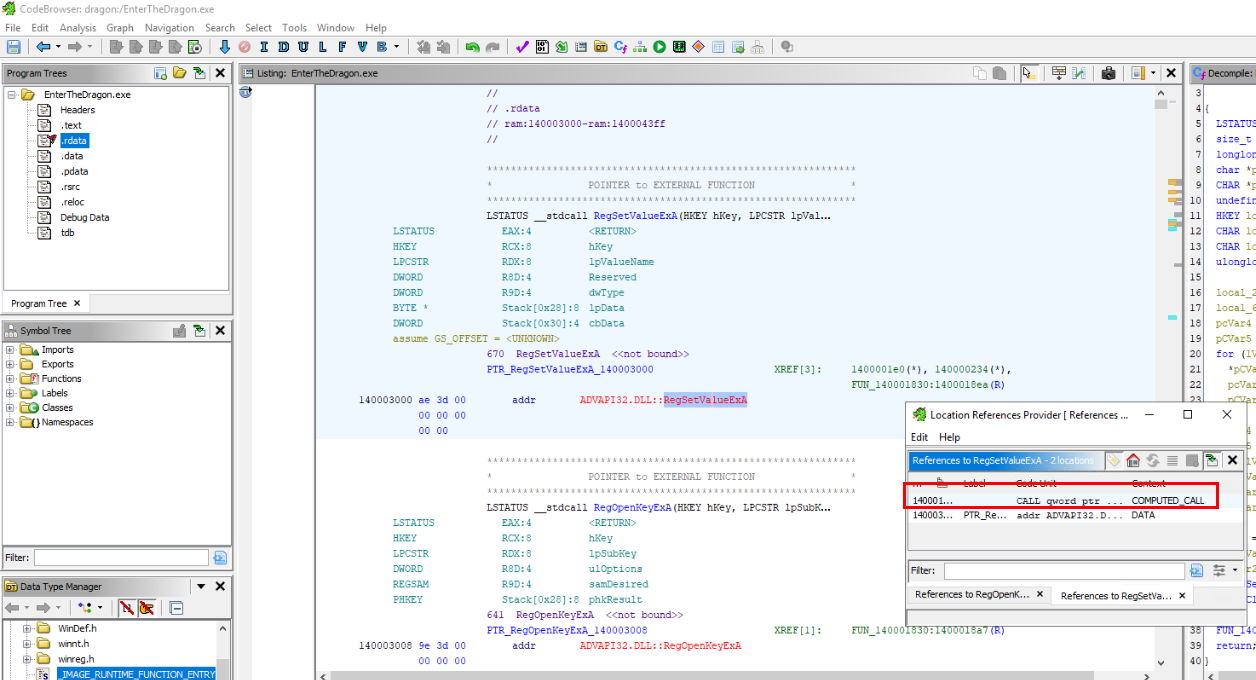
We can trace reference of RegSetValueExA to find the function calls and arguments pass to this function.
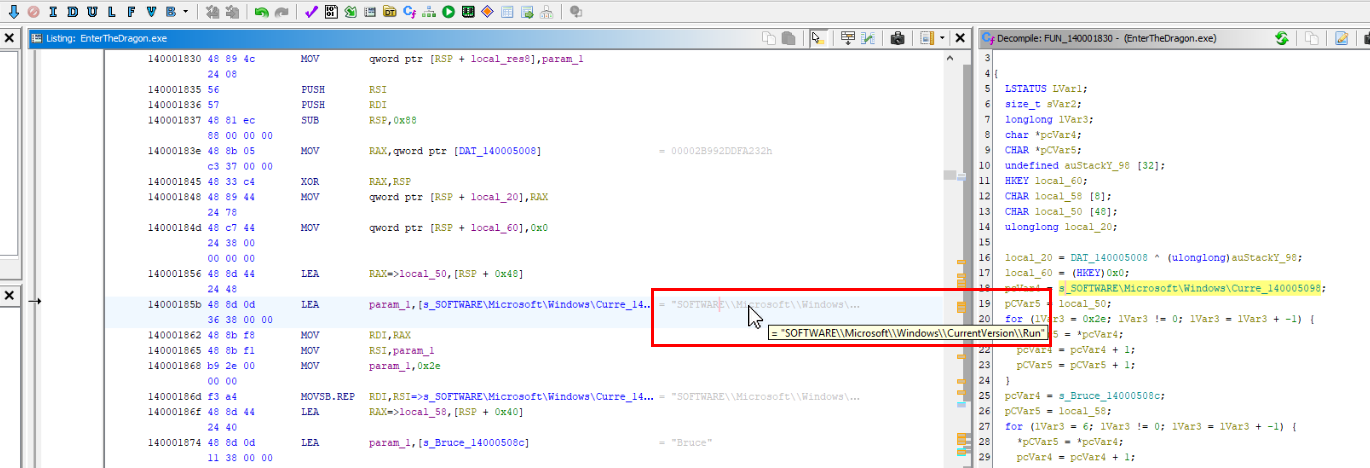
Then we can see that the sample will make itself persistence by adding a key to the infamous run registry key.
Answer
SOFTWARE\\Microsoft\Windows\\CurrentVersion\\RunQ15) What is the name of the key that holds the persistence value? (Format: String)
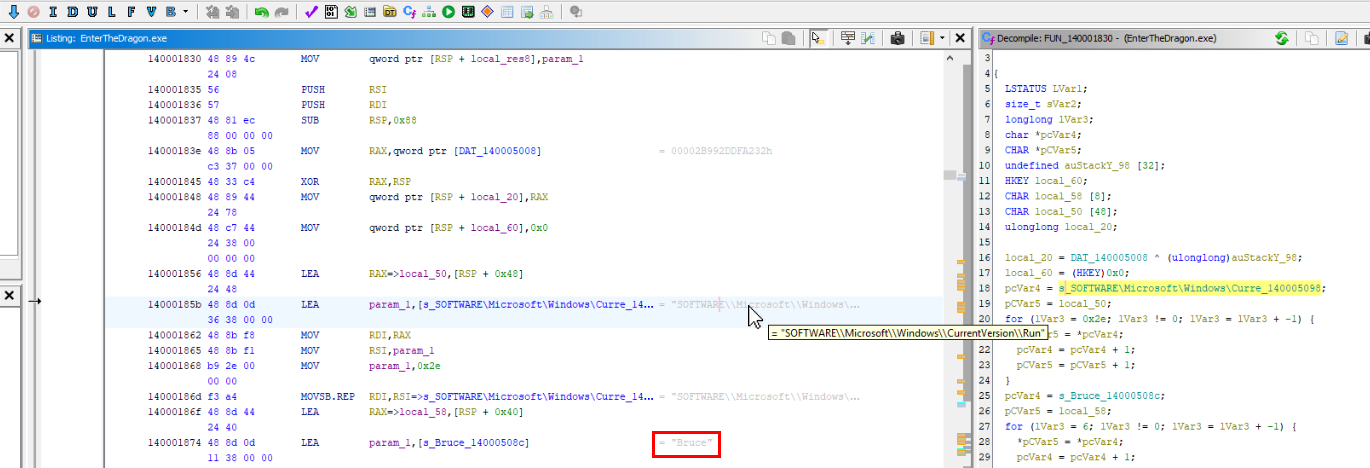
And the value that of the key is "Bruce" which should come from "Bruce Lee"
Answer
Bruce https://blueteamlabs.online/achievement/share/52929/162
https://blueteamlabs.online/achievement/share/52929/162
Summary
A static malware analysis was conducted to analyze Bruce Lee theme malware which has many capabilities such as detecting debugger, creating a mutex, read files from the internet and create registry key for persistence.
IOCs
6932ff601d9b00fc59d773332518cbd0https://pastebin.com/AsasW19vBoardsDontHitBackSOFTWARE\\Microsoft\Windows\\CurrentVersion\\Run\\Bruce